Blog
Secuni Joins Forces with Minuteman
On July 1, 2024, Secuni was acquired by Boston-based Minuteman Security & Life Safety.
For our clients, we believe that this will be a very positive development.
- Your entire account team and technicians are staying in place, along with all Secuni senior management.
- With our greatly expanded geographic reach, we will be able to serve our clients with multiple sites more directly and effectively.
- We will have expanded technical capabilities and greater access to more product lines.
We knew that Minuteman was the strategic move for Secuni because the two companies share the same values: delivering innovative and engineer-designed security and safety solutions for long-term value, and providing extremely attentive and adept service.

Over the coming days, we will be calling you to discuss how this change benefits your company, and answer any questions. In the meantime, we have provided answers to a few FAQs. Feel free to contact us anytime about this news.
FAQ
Who is Minuteman?
Headquartered in the Boston area, Minuteman Security & Life Safety is a privately-held provider of enterprise security system technology solutions, including custom design, installation, development, and support services. Like Secuni, Minuteman has offered a diverse range of advanced security management systems, including video surveillance, access control systems, emergency communications, intrusion detection systems, and public safety security solutions.
Where does this new combined company operate?
In addition to Secuni’s home area of New Jersey and its offices in New York, Florida, Virginia, and Pennsylvania, we also have a physical presence in Connecticut, Illinois, Maine, Massachusetts, New Hampshire, North Carolina, and Vermont. We also have a Program Management Office that oversees national and global clients.
As a Secuni client, is there anything I should do differently?
Not yet – please continue to work with us as you currently do. Your Secuni account team will remain in place, with the same phone numbers and email addresses. Place new orders and service calls in the same way. Over time, we will make some workflow changes but will tell you well in advance about any material changes.
What exactly has changed with this transaction?
Dynamic Security LLC, which since August 2023 has operated under the brand name Secuni, has been acquired by Minuteman. Dynamic Security LLC dba Secuni is now currently operating as a subsidiary of Minuteman.
What do my accounting colleagues need to know?
In the short- and medium-term we will continue to conduct financial and contractual matters as Dynamic Security LLC, with the same EIN. Our AR and AP team members will call your accounting colleagues well in advance of the day when changes are needed.
I still have questions!
Send us an email to info@secuni.com, or use the chat widget in the bottom right corner of the site.
The Press Release
Minuteman Security & Life Safety Acquires Secuni
Andover, Mass. — July 22, 2024. Minuteman Security & Life Safety (“Minuteman”), a leading super-regional provider of integrated security, communication, and life safety systems, today announced that it has acquired systems integrator Secuni of Edison, NJ.
With the acquisition of Secuni, a well-established integrator with an experienced managed services team, Minuteman expands its coverage of the U.S. East Coast and its ability to service enterprise clients globally. The combined company’s engineers and field technicians now operate out of 24 office locations on the East Coast, and its Program Management Office supports national and global clients.
Secuni, formerly known as Dynamic Security, has been providing enterprise security technology solutions for more than 20 years under the leadership of General Manager Barton Kartoz and Vice President Victor Alexander. Secuni employs more than 60 professionals among five offices in New Jersey, New York, Pennsylvania, Virginia, and Florida. Bart, Victor, and the entire Secuni team will continue to grow the firm’s operations and support client relationships.
Minuteman CEO Joe Lynch said, “The Minuteman mission is to improve security and safety for our clients from Maine to Florida and beyond, and this acquisition helps us enormously. We’re particularly excited to offer Secuni’s Managed Services capabilities together with our Program Management service, so global security leaders can achieve a centrally-managed and consistently high level of security system performance for all their sites. Secuni also has a lot of talented young engineers, who have recently designed innovative custom safety & security solutions for industrial and pharmaceutical multinationals.”
Secuni General Manager Barton Kartoz remarked, “This is such a natural combination. Both Minuteman and Secuni believe in empowering engineer-led teams to deliver client solutions that are built for long-term value. We will also now be able to directly support Secuni clients far beyond our core New Jersey territory, with added access to Minuteman’s global Program Management team. We’re also excited to leverage Minuteman’s advanced kitting capabilities and innovative open-architecture license plate recognition system.”
The combination was effective July 1, 2024.
About Minuteman
Minuteman Security & Life Safety, headquartered in Andover, Massachusetts and founded in 1988, is a leading provider of enterprise security and life safety technology solutions. Our services are utilized by a wide range of organizations throughout the United States. Our wide-ranging client base includes high technology, law enforcement, critical infrastructure, defense, mass transit, large retail, academic institutions, public safety agencies, and healthcare institutions with locations throughout North America.
About Secuni
Secuni is a technology integration firm that solves physical security problems, primarily for industrial and commercial firms, schools, and brand-centric organizations. Founded in 1999 and headquartered in Edison NJ, the company has five offices across the Eastern US. Secuni’s open-architecture focus and engineer-driven design/build approach has powered the company’s expansion among large global enterprises, heavy industrial firms, and schools.
A novel solution for interlocking doors
We recently built a new access control solution for a life sciences company’s sterile lab environment, using a particularly elegant technical approach.
This client’s 10-room clean area included multiple interlocking doors with and without card access, and one three-door interlock. In this application we were asked to account for omni-directional and bi-directional traffic for areas of gowning, de-gowning, material handling, waste handling, and pressurized cross-contamination.

Customarily, a piece of hardware such as Von Duprin’s 9400 series interlock controller could be used to interlock multiple doors. These tried-and-true controllers offer several attractive features like expandability and a FAI (Fire Alarm Interface) input. (Both require additional hardware). In the case of multiple interlock spaces, each would need a dedicated controller and FAI input. Interlock controllers also need a sizable amount of space local to the doors and a dedicated high voltage power source.
One feasible alternative to that method would be to use an access control platform such as Genetec to collect a variety of inputs, and create a custom macro to determine the sequence of operations. The access control platform method is effective if your software interface allows enough flexibility to handle the programming. Yet the additional hardware costs and lack of open-ended programming on systems like Lenel and Software House make it hard to develop a standard process.
Secuni’s engineers instead developed a new solution utilizing PLCs (Programming Logic Controllers) designed by Automation Direct.
PLCs are typically utilized in HVAC and BAS systems. These small format modular units can be nested neatly inside of a power enclosure. The PLC utilizes the low voltage (24v) provided by any ACP to supervise inputs from several sources including door status, bond status, entry/exit requests, emergency over-rides, and any other environmental condition (pressure/temperature/vapor detection) which can be indicated by outputs from external devices.
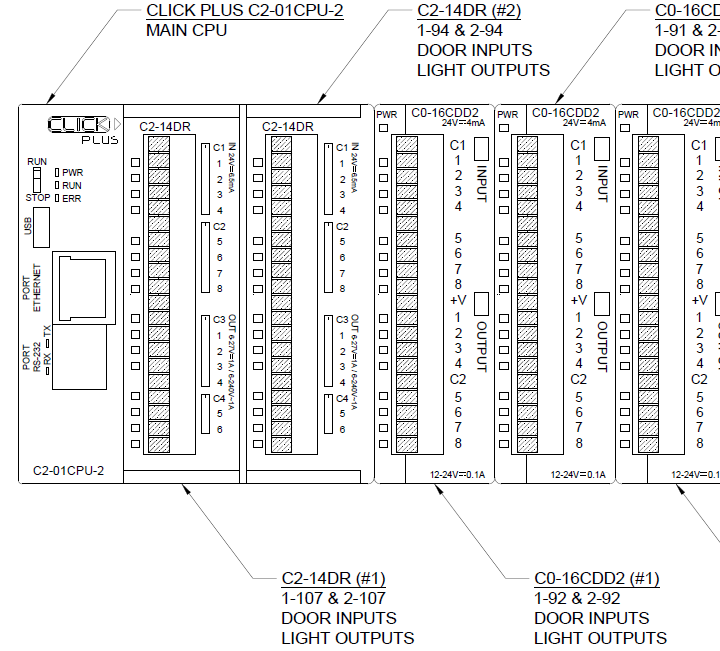
Here’s a partial schematic from our as-built drawing, showing the PLCs.
PLCs collect analog or digital input signals from multiple devices. These “events” can then be used to write custom programming sequences, which produce “actions” in the form of digital or analog outputs.
This approach allows for a consistent standardized approach to complex interlock solutions regardless of access control platform. PLCs also offer a significant cost reduction on the hardware side. Card access doors will still require a door controller, but non-card access doors will not require additional licensed hardware.
Cost savings are case by case depending on scope and system but will be quite meaningful considering the lack of licensing, need for electrician, and hardware costs.
We believe this method saved the client $50,000 over the customary interlocking door technical approaches.
PLCs can be monitored via network connection or function completely off-line in areas of concern. PLCs can also live on a BacNet protocol for automations integrations or be linked on a RS-485 Comm protocol.
One CPU can handle up to 8 downstream controllers, which means 8 interlocked areas with basic config.
PLCs programming can be stored onboard the CPU with back-ups loaded on the mounted SD slot or USB stick. Programming can be done directly via network/serial ports or remotely via IP interface.
AI in Security: Part 1 of 2, the Short-Term View
One year ago, ChatGPT went mainstream and started the AI hype train. Security technology manufacturers jumped aboard, promoting AI-driven improvements in video analytics and security software user interfaces.
So is your job about to get meaningfully easier because of AI?
Not really.
As with any major new technology, people generally overestimate the short-term impact.
Based on what we saw at ISC West 2024 and in speaking with vendors and our clients, here is our take on the short-term:
You will soon be able to use more natural language in searches like “Show me the White Tesla S3 in parking lot B last week”. This is somewhat better than using dropdown lists, and we don’t begrudge UI improvements. Other queries like “What time did Amy Cooper leave on Monday?” just don’t move the needle enough. We will get interested when we can ask “Show me the most recent car collisions” without seeing false positives and missing events. But noone is advertising that yet.
As reported by IPVM (paywalled post) and seen by our own ISC West attendees, the new “AI” product enhancements are mostly smoke. The Best New Product winner couldn’t find a “garbage can” in a video search, and a search for “smoke” returned BBQ grills. Another product mistook hands and phones for guns. So far this seems more like rebranded analytics in beta.
Where we see some short/medium-term AI promise is in smarter tagging and analysis of security datasets. By dataset that we mean the people & objects in the video, access control entries/exits, and other sensor data like temperature. With clean tagging and good analysis (two different things!), then you could ask, “Show me the anomalies.” Better yet, the system will proactively tell you about the potentially worrisome stuff.
Alas that’s a few years off from being reliable, and these engines are going to need your own site-specific training effort to handle “permitted exceptions” like shift changes.
While we are skeptical about the short-term impact of AI on your security solutions, it’s going to eventually help. After all… with any major new technology, people generally underestimate the long-term impact.
How You Can Respond to the Flipper Zero Threat
A $100 handheld consumer-friendly device named the Flipper Zero got our attention in 2022, when its Kickstarter was a viral success.

Its continued popularity more recently got the attention of the New Jersey government, who correctly called it a potential threat to any company or school with access cards.
For those new to the topic: In the hands of a moderately tech-savvy person, it can be configured to copy the digital credentials from someone else’s access card. This almost always happens without permission. Once the other person’s credentials are on the Flipper Zero, then the bad actor can gain unauthorized access to your premises.
Card-copying, an established technology, is now packaged in consumer-friendly devices and thus much more of a threat to certain access control systems.
125kHz “Prox” card systems are the most vulnerable and you should plan your eventual migration away from them.
The most popular upgrade path is to switch over to 13.56MHz “Smart” cards, which come in various crytographic strengths:
- NXP’s Mifare Classic/Plus/DESFire/DESFireEV3
- HID’s iClass Legacy/SE/SEOS
At this writing, the first two of each type have been cracked. DESFireEV3 and SEOS are the most secure.
We can help review your card access system vulnerabilities, and create a roadmap to a more secure state.
Roadmap Considerations
Card Readers. You may need to upgrade the readers at each door, replacing or reprogramming them with multiclass readers which handle both kinds of cards (Prox and Smart) and mobile credentials. New cards can be issued once all the readers are installed and active, and the prox cards disabled. The capital expenditure can be spread out by doing it in stages, which can be somewhat more complicated in large-population corporate campuses and universities.
Credentials. Physical cards are a good solution, but the case for switching to mobile credentials has been improving. They are fundamentally more secure than cards (with two-factor authentication), can be provisioned remotely and in stages, and are more extensible. Mobile makes sense right now for smaller organizations (in terms of doors and people), but the economics at scale has been improving quickly.
Multipurpose cards. Universities and colleges often issue cards that work for doors, lockers, POS/vending, the library, and so on. It’s very convenient for the user, but moving to a less-crackable card system takes more effort to get the systems in sync.
High-traffic areas. The low-latency symmetric encryption in the vast majority of card access systems allows people to move through turnstiles quickly. Mobile credentials act somewhat slower, which may be a concern for high-flow areas. We are seeing good biometric (face identification) solutions in the market, and over time expect less user resistance to the technology.
How We Choose Technology Suppliers
Picking physical security technology suppliers has never been more complex than it is today, and it promises to get only more difficult given the number of new and exciting technologies being developed – and the number of manufacturers and distributors hawking them.
Last year, Secuni used more than sixty suppliers. Of course, some are central to a solution while others provide just a few peripherals. To be an effective design-build outfit, management of supply chain is an important part of our success. Not all the new suppliers will be successful, and we do not want to strand you with obsolescence. The biometrics and analytics markets are littered with skeletons of defunct companies.
What are the key factors for us?
- We are hesitant to adopt new suppliers without extensive field testing. We also feel it is fair to ask new suppliers for financial bona fides to establish their potential longevity as a going concern.
- Product support is a massive difference-maker: we expect thorough sales support, and training for both ourselves and our clients.
- Open architecture is key. We do not advise our clients to invest in full solutions because there are so many great open-architecture software developers. That flashy feature from the closed system will soon be copied by others and be available to most of the open-architecture market.
- Commitment to current and emerging standards, like ONVIF and OSDP.
Our own team knows that we can’t represent every good product. To maintain expertise, we limit ourselves to a set of solutions that we feel satisfy different market needs, while recognizing that we cannot address all needs – and that many of the suppliers we don’t represent have great products that solve client problems very successfully.
This helps us stay grounded and tuned into the reality that although product selection is important, it’s ultimately the implementation and operational teams that create successful outcomes more than specific product features.
We also encourage our clients to spend time in the selection process. Consider how many hours you will spend operating the system after selection! The upfront investment of time, while hard to find for most of us, is critical to ensure the best fit. Often, during the selection process, we uncover important additional requirements that help the vendor selection process.
Secuni’s charitable activities, and a spotlight on river blindness
We regularly make financial and in-kind gifts to organizations who perform good works.
Perhaps the highest-leverage use of our charitable dollar belongs to the United Front Against River Blindness (UFAR).

This NGO is currently delivering river blindness treatment to tens of thousands of people in the Democratic Republic of Congo — for about ten cents a dose. This Nobel prize-winning pharmacological treatment is now preventing many Congolese from going blind, thanks to the efforts of UFAR and pharmaceutical giant Merck.
UFAR held their annual fundraiser last week, and Secuni was pleased to make a donation to UFAR.
MEDIA RELEASE
For Immediate Release: October 23, 2023
Secuni Supports Eradication of River Blindness with Charitable Support to Leading NGO
Edison NJ — Secuni, a security technology integrator and services company, announced that it has made a donation to the United Front Against River Blindness (UFAR). The company’s support at the UFAR Champion level allowed 10 undergraduate students to attend UFAR’s 13th annual Soiree Saturday benefit on October 21st at the Marriot Forrestal Hotel in Princeton, NJ.
UFAR is a non-profit organization dedicated to combating five priority Neglected Tropical Diseases (NTDs), including river blindness, that affect millions in the Democratic Republic of Congo. The organization was founded by Dr. Daniel Shungu, a renowned medical researcher and humanitarian.
The event’s keynote speaker and honoree was Mr. William I. Campbell, Chairman Emeritus of The END Fund. Mr. Cambell pointed out that eradicating these diseases is one of the lowest cost ways to make a large impact on the human condition. Mr. Cambell singled out UFAR as being in the most effective tier of NGOs because UFAR treats individuals against river blindness (Onchocerciasis) for about 10 cents a dose.
“It was an inspirational event,” said Barton Kartoz, General Manager of Secuni, “and one must commend UFAR and The END fund for their collective efforts to alleaviate the suffering of millions through low-cost pharmceutical interventions.”

If you would like to learn more about UFAR, write to ufar@riverblindness.org or info@secuni.com.
Dynamic Security is now Secuni: The FAQ
On August 10, 2023, our company began operating publicly as Secuni.
We have selected the new name to reflect our steady expansion beyond security technology integration, to include managed services and the unification of systems that solve a company’s security, safety, and operational requirements.
Secuni at Age 24
Our company turned 24 this year.
And like a college graduate with some real-world experience, we’ve got a fairly developed sense of how we work with others and make decisions.
Centralizing Your Security Systems
It’s common for large companies with multiple facilities in the US (and overseas) to have a fragmented set of security systems at all those sites. You might have several kinds of video surveillance solutions running at the same time, and access control systems that don’t talk to each other or your HR database.
How Managed Services Improve Your Security System’s Uptime
This is part of our series on how a managed services team helps your system deliver the required level of corporate safety and security.
(If you’re new to this series, a third-party “managed services team” is a remote set of security experts who assume responsibility for your security system’s day-to-day operation. Here’s our team.)
Today, we’ll focus on how they help deliver a high level of system uptime.
